Cybersecurity Threats
This page covers two of the four main categories of cybersecurity threat: hacking and social engineering. To understand malware and denial of service attacks, click here.
What is Hacking?
Hacking is when someone tries to gain access to a computer or data without permission of the owner. This could be by…
- using sophisticated techniques to find flaws in software, allowing access
- guessing someone's password
- using malicious software
- repeatedly trying different passcodes until the correct one is found (a brute-force attack
Different types of hacker
There are three types of hacker. One is illegal, one is not illegal, and the other…?
Black hat hackers
These are the bad guys!
- They are non-ethical and hack maliciously
- Make money by selling stolen data or blackmailing the data owner
- May cause damage for fun or to prove a point
- They act illegally and can be prosecuted!
White hat hackers
These are the good guys!
- They are ethical
- Hired by the organisation they’re trying to break in to
- Act professionally and do not cause damage
- They perform penetration testing, checking a system to see if a malicious hacker could gain access and, if they can, how much damage they could potentially cause
- They act legally because they have permission from the system owner
Grey hat hackers
These are somewhere between black and white hat hackers
- They are ethical
- They will hack into a system without permission, but won't cause any damage or steal data
- Their motivation is to claim a "bug bounty" for reporting vulnerabilities to the system owner
- They act illegally and can be prosecuted (but probably won't be)
Social Engineering
Computer systems are usually very well protected against hackers. Often, the easiest way to get into a system is to trick a legitimate user into giving them access. This is called social engineering, and there are lots of sneaky techniques!
Types of Social Engineering
Click a button to reveal information about each technique.
Phishing
Baiting
Pretexting
Quid Pro Quo
Scareware
Shoulder Surfing
Phishing

Fake messages (like an email or text) pretending to be a real company to try to trick you into giving personal information.
Example:
- An email which looks like its from your bank, saying you need to urgently check your account – but the link takes you to a fake website
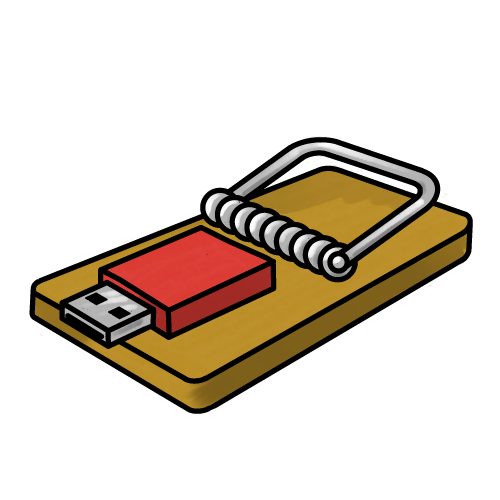
Baiting
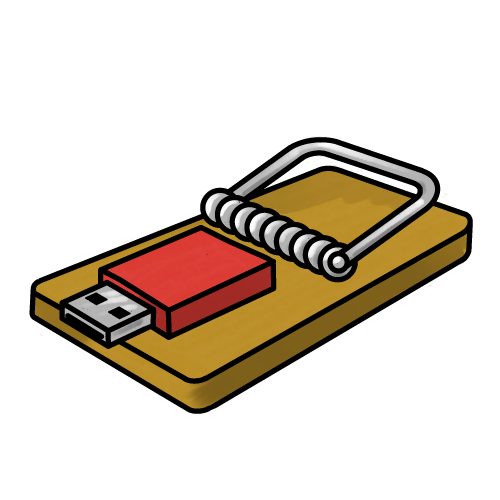
Attackers give victims the opportunity to get something for nothing, or for a reward – this is the bait!
Examples:
- A malware-infected USB stick, labelled “confidential”, is left in a public place. Someone plugs it into their computer and unknowingly installs malware
- A fake website offers a mod for a game. Users install it, but it really gives the attacker access to their system
Pretexting
A person pretends to be someone they’re not to get private information from you.
They make up a fake story (a pretext) to trick you into trusting them.
Examples:
- Someone pretends to be from IT support and says they need your password to "fix your account.".
- A person calls saying they’re from the bank and asks you to "confirm your details".
Quid Pro Quo
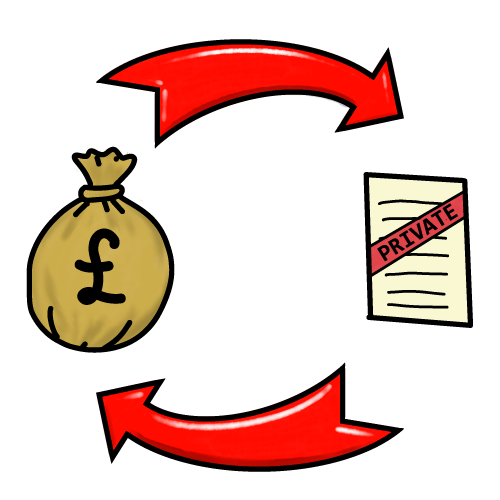
Quid pro quo is when a person offers you something, like help or a reward, but they secretly want information or access in return.
It means "something for something".
Examples:
- A hacker pretends to be tech support, saying: "I’ll fix your computer if you tell me your login details".
- A person says they’ll give you exam answers if you send them private files from the school network.
Scareware

Scareware is a trick that tries to frighten you into doing something, like downloading a fake program or paying money.
It uses scary messages to make you think your computer is infected, even when it’s not.
Examples:
- A big red pop-up says: "Your computer has 57 viruses! Click here to fix it!", but the link actually downloads malware
- A fake website shows a warning that looks like it’s from Windows or antivirus software, asking you to buy or download something to "remove the threat."
Shoulder Surfing

Looking over someone’s shoulder to see them typing passwords or other sensitive information
More high-tech examples include:
- Cameras hidden above keypads
- Card skimmers, which copy your bank card details, placed over cash machine card slots